Analyze Cyber Risk in Interconnected Systems
Learning Objectives
After completing this unit, you’ll be able to:
- Explain the impact of interconnected-system disruptions on business operations.
- Describe the shift to managing cyber risk in interconnected systems.
The New Face of Disruption
According to the Global Cybersecurity Outlook 2026, “A new generation of cyber incidents has exposed the fragility of these connections… where a single local fault or targeted attack can rapidly cascade into global scale consequences.”
On a normal Tuesday morning, an HR manager at a Fortune 500 company finds the third-party payroll system inaccessible. This forces the manager to issue an immediate company-wide communication about the delay. At a small community hospital, a clinic manager manually reschedules several patient appointments when an external booking platform suddenly becomes unavailable. At a large distribution warehouse, a retailer pauses all restocking operations because inventory data from a cloud-based supplier is temporarily locked down.
These disruptions don't entirely stop work. Instead, they alter plans, create uncertainty, and force employees to wait for clarity from systems they don't control. Ultimately, these disruptions translate into lost productivity, delays, and significant financial costs, underscoring why managing cyber risk is a critical business imperative.
Those closest to the work would not typically label these as cyber incidents, as they lack the obvious, technical indications of an attack (no locked account, suspicious popup, or unexplained file movement). The experience is like sitting in heavy traffic; they feel the slowdown and the uncertainty, but the stalled vehicle miles away that caused it is invisible.
While cybersecurity professionals might investigate and classify these disruptions as incidents, for most organizations and individuals, cybersecurity is experienced through delay, disruption, and uncertainty rather than technical diagnosis. To understand why these disruptions feel more frequent and harder to contain, it helps to look at how modern systems are connected.
Cyber Risk in Interconnected Systems
“Cybersecurity is accelerating amid growing threats... even as governance frameworks and human expertise struggle to keep pace.” —Global Cybersecurity Outlook 2026, p. 4
Disruption caused by cyber incidents is not new. What has changed, as described in the World Economic Forum’s Global Cybersecurity Outlook 2026, is the environment in which those disruptions occur. This report emphasizes that in highly interconnected ecosystems, a cyber incident affecting one vendor or system can cascade across the entire organization. In this environment, cyber resilience underpins an organization’s ability to minimize the impact of significant cyber incidents on its primary business goals and objectives.
As organizations adopt AI, automation, and vendor-managed platforms, decision-making and service delivery depend on systems that operate across boundaries. When something goes wrong, the effects are immediate, even if the system executing the action is outside the organization experiencing the impact.
When it’s unclear where an issue originated across interconnected systems, maintaining visibility and accountability becomes difficult. Organizations rely on systems they do not own and don’t necessarily have visibility into, and important decisions are made outside their direct control. Consequently, business teams experience delays and interruptions while waiting for security or IT to determine the cause.
The table below outlines the main categories of cyber risk in interconnected systems and shows how each can undermine operational stability when dependencies and automated decisions are not fully visible.
How Cyber Risk Behaves in Interconnected Systems
Risk category |
Impact and management challenge |
|
|---|---|---|
Automation and AI |
Sudden service/workflow disruptions: Decisions are made before teams fully understand the automated cause. |
|
Third-party dependence |
Delays or outages without quick fixes: Systems are owned by external vendors, not by the organization. |
|
Cybercrime |
Service interruptions: The incident often looks like a business failure, not a security event. |
|
Supply chains |
Issues cascade across many companies: No single team has full control or visibility into what went wrong. |
|
Regulation |
Slower responses or paused operations: Rules struggle to keep pace with fast-changing systems and tools. |
|
Inequity |
Greater impact and longer delays for smaller teams: Risk disproportionately affects those least able to address it. |
|
Trust fragmentation |
Confusion in standards/coordination: Inconsistent standards make coordination and decision-making harder. |
|
In interconnected systems, risks often surface only after they disrupt the flow of work. What appears technical on the surface can quickly affect operational stability and decision-making, reinforcing the need for shared visibility, clear ownership, and coordinated resilience.
A Coordinated Response
“Ultimately, strengthening collective cyber resilience has become both an economic and a societal imperative” —Global Cybersecurity Outlook 2026, p. 4
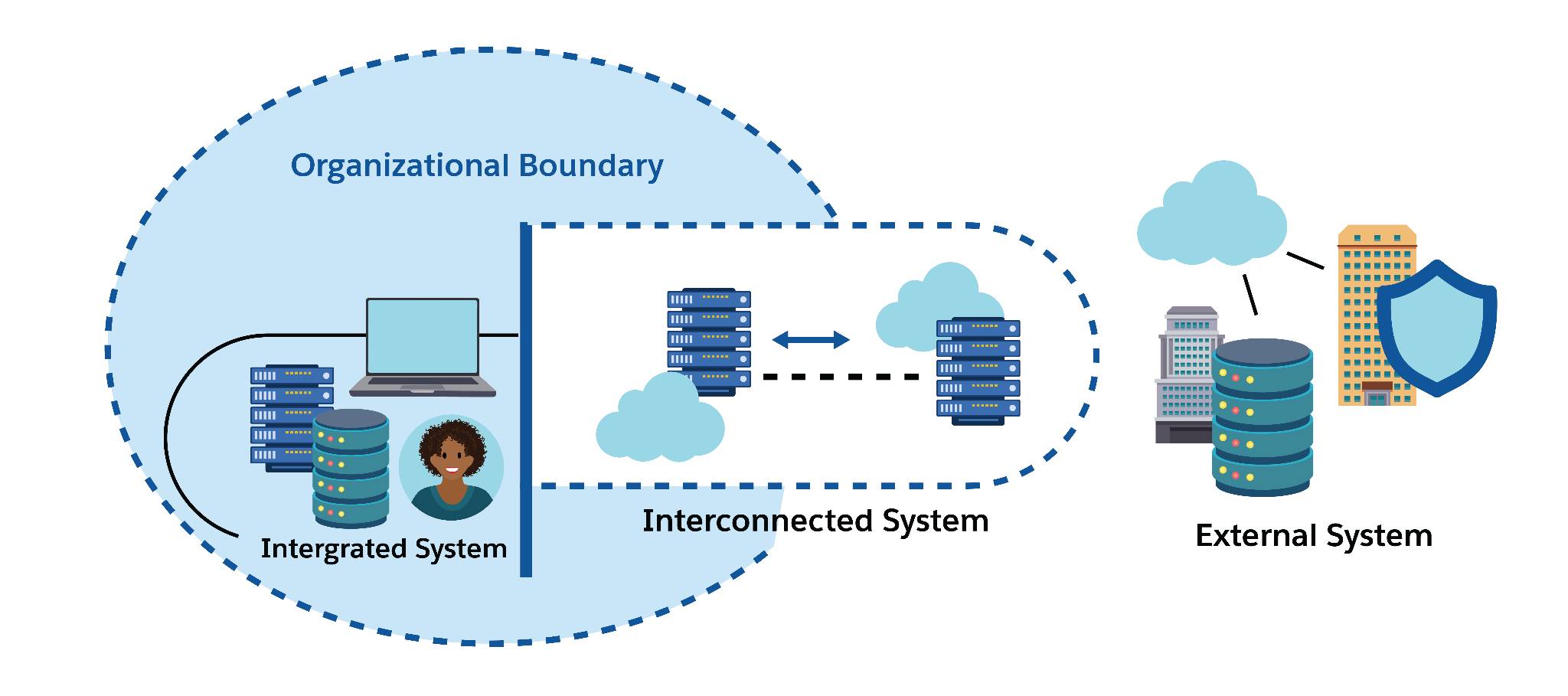
In cybersecurity, interconnected does not simply mean systems are linked. It reflects a reality in which business operations depend on systems, data, and services that extend across organizational boundaries and are not always under direct control. Some systems are internally integrated and managed within the organization. Others exchange data and functionality with external platforms or vendors. Together, these relationships form an ecosystem in which disruptions can cascade beyond a single system or team. Each connection introduces interdependent risk and requires coordinated responsibility.
Regarding these risks and responsibilities, the Global Cybersecurity Outlook report makes one point clear: No team can manage them alone. As ransomware, fraud, data leaks, and AI-related vulnerabilities accelerate, cybersecurity depends less on isolated controls and more on shared visibility and coordinated action across interconnected systems.
The table lists key resilience practices, explains their purpose, identifies the risk they address and recommends Trailhead resources to help build capabilities in interconnected systems.
Resilience Practice |
Purpose |
Risk(s) Mitigated |
Trailhead Resource To Help Build This Skill |
|---|---|---|---|
Shared Language |
Ensures internal teams and partners talk about risks the same way so decisions are clear |
Confusion or miscommunication that leads to gaps or delays in protection |
|
Increased Visibility |
Helps teams see what’s going on across connected systems so problems show up early |
Blind spots that enable threats to go unnoticed, especially from external systems or suppliers |
|
Early Involvement |
Brings security into decisions early so risks are addressed before they disrupt operations |
Major fixes late in the process or implementing insecure systems that cause problems later |
|
Shared Response |
Sets up clear, fast ways for everyone involved to act together during an incident |
Slow or disorganized incident responses that let problems worsen or spread |
|
Shared Learning |
Establishes a process to use security incidents for updating internal controls and processes |
Repeating past mistakes or failing to fix common, underlying system vulnerabilities |
Together, these practices embed resilience into everyday operations, helping organizations maintain visibility, accountability, and confidence across interconnected systems.
Sum It Up
Cyber risk today spreads across systems, vendors, and automated decisions in ways that are not always immediately visible. Managing that risk takes more than strong tools or fast fixes, it demands awareness, clear ownership, and coordinated action across interconnected systems.