Learn About Threat Intelligence
Learning Objectives
After completing this unit, you’ll be able to:
- Describe the goals of threat intelligence.
- Explain how threat intelligence is used to prevent or mitigate attacks.
- Explain the different types of threat intelligence.
- Describe the different types of threat intelligence roles.
What Is Threat Intelligence?
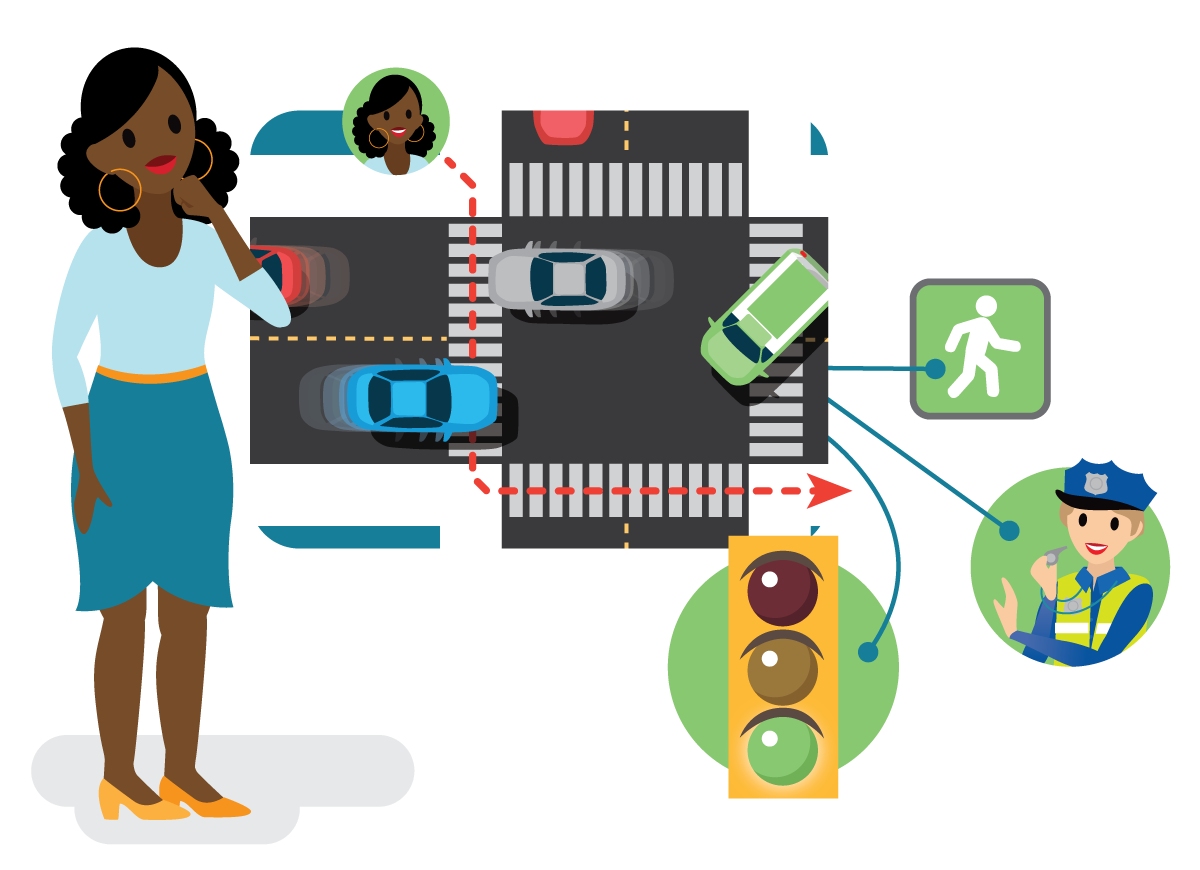
The goal of threat intelligence is to identify any potential event that would cause harm to ourselves or our work. The process of identifying and analyzing threats is not new to us. For example, crossing a busy street is fraught with possible dangers. But we are able to do so safely, identifying threats, such as a motorist in a speeding car, and taking measures to minimize harm. We rely on our prior knowledge as well as processing new information. We take into account environmental factors (weather conditions), social norms (using the crosswalk), and the role of possible allies (authorities enforcing speed limit restrictions).
In the same way we evaluate threats when crossing the street, we use threat intelligence to identify and analyze cybersecurity threats. The computing ecosystem is fraught with attackers looking to exploit vulnerabilities in your systems to steal your information.
As a threat intelligence analyst, you review these potential threats to better understand the types of tactics, techniques, and procedures (TTPs) that adversaries may use to compromise your systems. You take into account the type of industry you work in, the behavior of both external adversaries as well as trusted insiders, and the resources you have available to help counteract weaknesses in your systems.
How Do I Use Threat Intelligence?
Threat intelligence boils down to knowledge, rooted in data, that helps you spot trouble and take action to bolster your organization’s security. Threat intelligence is made up of the simple ingredients of evidence-based and action-oriented advice about an existing or emerging menace to assets. It leads to informed decisions about your security.
One way to think about threat intelligence is in the classic principle of who, what, where, when, why, and how that detectives use to solve crimes.
-
Who is attacking you?
-
What kind of damage does this attack inflict?
-
Where did this attack originate?
-
When did the attack begin?
-
Why are we being attacked?
-
How was the target compromised?
The clues you look for to answer these questions are called indicators of compromise (IOCs). For example, you might analyze email addresses, email subject lines, and links to detect phishing attempts. Other IOCs can include IP addresses, domains, URLs, hashes, strings, and accounts.
In researching these questions and sleuthing out IOCs, you follow the five steps of the intelligence cycle.
Step 1: Ask Questions
Ask questions about security events, and gather data from internal sources, such as network logs and incident response reports. You also look at external data such as the open web, dark web, technical reports, and other sources such as information sharing groups.
Step 2: Organize the Data
Organize the data and use automated tools, like a Security Incident and Event Management (SIEM) solution to correlate information. Use data pivoting to connect the dots, and identify gaps in your intelligence so you can make better decisions about how to fill those gaps. Pivoting involves starting with a reliable data point and allowing it to guide you through the next steps in your analysis. For example, you may pivot from a given indicator, like a known malicious email address, to an adversary, which may lead you to a previously detected campaign.
Step 3: Analyze the Data
Analyze the data for potential security issues. You rely on rigorous ways of thinking that use structured techniques to identify biases and uncertainties. You don’t just reach conclusions, you also think about how those conclusions are reached. This is where you really put the intelligence in threat intelligence.
Step 4: Report the Findings
Report the findings to the relevant teams. The intelligence you produce may be used for incident response, security operations, vulnerability management, risk analysis, fraud prevention, or security leadership. It can be in the form of a memo, presentation, newsletter, or technical information feed.
Step 5: Gather Feedback
Gather feedback from the consumers of the intelligence you produce to determine whether relevant questions were answered, or whether further investigation is needed. Then the cycle begins again; your work here is never done. Hooray job security!
Types of Threat Intelligence
Not only do you need to understand how to gather information using the threat intelligence lifecycle, but you also need to know the difference between different types of threat information. Let’s take a closer look.
-
Strategic threat intelligence forms a picture of the intent and capabilities of malicious cyberthreats. You identify patterns and emerging threats and risks, in order to inform decision- and policy-making. This type of threat intelligence assists stakeholders in making security-conscious decisions related to big-picture items, such as mergers and acquisitions and where to prioritize investment of mitigating controls. Typically the audience of this form of intelligence is the leadership team or board.
-
Operational threat intelligence informs day-to-day tasks. You use this type of intelligence to develop signatures and IOCs to assist your security operations staff in alerting and blocking new threats. This also includes researching zero day (previously unknown) threats to look for weaknesses before they have the chance to be exploited. You then deliver this information to the threat-hunting team so they can proactively search for malicious actors on the network. Typically, the audience of this form of intelligence is security operators, such as incident responders and detection engineers.
-
Tactical threat intelligence is highly specialized, technically focused intelligence to guide and support the response to specific incidents, campaigns, or malware. This is usually provided in the form of threat actor profiles, malware reports, and internal and external threat trends. Typically, the audience of this form of intelligence is the information technology (IT) team, teams that manage preventative controls, and detection teams.
Types of Threat Intelligence Roles
The role and tasks you perform as a threat intelligence analyst will vary depending on the type, size, and sector and maturity of the organization and security program in which you are employed. You may work in a threat intelligence role that provides a service to a broader community, such as at a security services company providing threat intelligence research and reporting to customers. Analysts in this type of role are usually tasked with tracking threat actors or performing research.
Alternatively, you may work on an in-house threat intelligence team at a software company, a government agency, or a media company, for example. In this role you identify threats facing a specific organization or industry.
In the units that follow, we cover the different types of responsibilities you can have as a threat intelligence analyst, regardless of whether you’re performing threat hunting for a highly specialized vendor, or producing operational threat intelligence for a small in-house security team. Read on to learn more about the importance of threat intelligence, no matter what organization or industry you work in.
The Importance of Threat Intelligence
Modern cyberattacks are sophisticated and well-funded and use highly targeted techniques. To stop attackers, organizations need to understand how the attacker operates, what their goals are, and under what conditions they will be successful. Answering these questions leads to solutions to prevent or mitigate attacks, and provides the context to understand their implication to your organization.
Once you understand your adversary, you can take decisive action to better protect your organization. For example, as a threat intelligence analyst at a technology company, you might provide leaders at a customer organization with strategic threat intelligence about a malicious state-sponsored actor that’s looking to target their systems in the time leading up to a national election.
Threat intelligence helps your organization detect existing and emerging threats to mitigate, as well as predict future threat sources and attack types. Doing so allows your organization to minimize security gaps that would leave the network vulnerable and protect against exploitation. It also helps change the organization’s and its employees’ behavior from reactive to proactive, further strengthening it against attacks, and enabling faster, more informed security decisions. For example, as a threat intelligence analyst at a software company, you might provide security operators with operational intelligence about IOCs associated with a new threat, helping them proactively defend the company.
Threat intelligence increases cyber resilience by testing protection strategies and assessing the organization’s susceptibility to compromise. It helps you prioritize defensive efforts to find the real threats to your business before they find you. It also helps the business implement strong risk management policies.
For example, as a threat intelligence analyst at a media company, you might supply the team that manages preventative controls with tactical intelligence about recent incidents targeting similar companies in your industry to help them make decisions about new policies to put in place to strengthen your organization’s protections.
And threat intelligence benefits everyone! It adds value for organizations of all sizes. Government leaders, executives, police chiefs, policy makers, IT specialists, law enforcement officers, security officers, accountants, terrorism and criminal analysts, and more can all get value from using threat intelligence to inform strategies and operations. What an exciting field to be a part of!
Resources
-
External Site: Center for Internet Security (CIS): What Is Cyber Threat Intelligence?
-
PDF: SANS: Quantifying Threat Actor Assessments
-
External Site: National Institute of Standards and Technology (NIST): Cyber Threat Intelligence and Information Sharing