ネットワーク侵入からの回復
学習の目的
この単元を完了すると、次のことができるようになります。
- ネットワーク侵入から復旧する方法を説明する。
- 通常業務に戻すために必要な条件を説明する。
ネットワーク侵入から復旧する
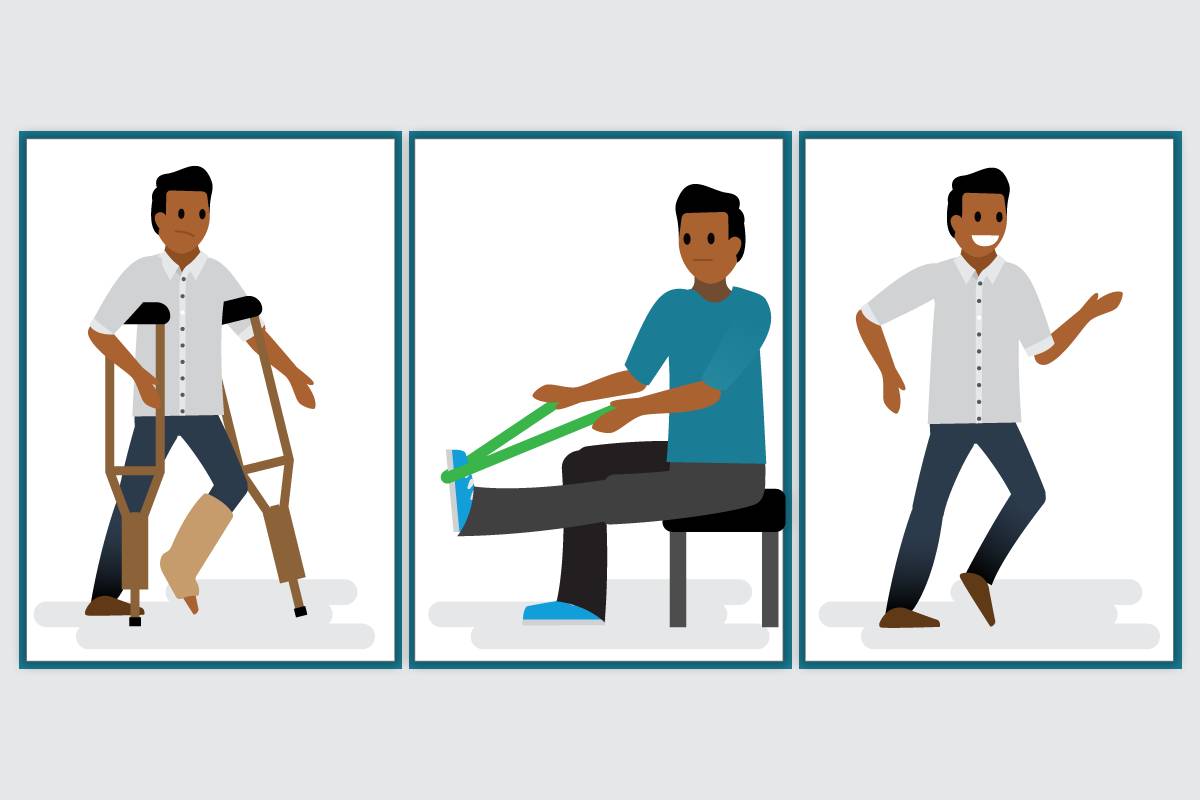
たとえば屋根から落ちて怪我をしたら、病院に運ばれ、そこから回復への道のりが始まります。まず、医者は診察やレントゲンなどで怪我の程度を調べます。骨が折れていれば、その部分をギプスで固定して動かないようにして治癒を促します。怪我が快方に向かってギプスが外れると、今度はリハビリで運動機能を回復させるように勧めます。怪我が完治して、骨折した部分も前より強くなると、治療は終わり、以前と同じようにジョギングやサイクリングを再開してもよいと患者に告げます。
医者が患者の怪我を診察して治療し、回復の手伝いをするように、セキュリティプロフェッショナルは、脅威を特定して検知し、影響を封じ込めて脅威を根絶して、今後の侵入に備えてシステムを強化します。ネットワークセキュリティエンジニアも、ビジネスがインシデントから通常業務に復旧するための手伝いをするという役割を担っています。
組織は、インシデントや自然災害から復旧するための事業継続計画を策定しています。この計画は、影響を受けたシステムやデバイスが復旧するためのガイドを提供し、通常の業務に戻れるようにするものです。
計画では、システムに優先順位を付けて、これらのシステムをいつ、どのように復旧させるかを定めた復旧時間と復旧ポイントの目標を記載しています。組織は、復旧時間目標 (RTO) を指定することで、事業を継続させるためには IT インフラストラクチャとサービスをいつまでに復旧させる必要があるかを明記しています。また、復旧ポイント目標 (RPO) を指定することで、データ消失の最大許容量を定めています。インシデントから復旧する場合、ネットワークセキュリティエンジニアは、ビジネスに不可欠なシステムから始めて、侵害されたデータを正常なバックアップに置き換えます。システムやネットワークの検証や、テストを実行して、システムが想定どおりに機能することを確認する場合もあります。
インシデントの後は、事後ミーティングを開催して、インシデントで得られた教訓を話し合います。この過程は、今後の脅威に備えてポリシー、プロセス、コントロールを強化するのに役立ちます。ネットワークセキュリティエンジニアは、ネットワークの回復力をより高めるための方法について、推奨事項を提案します。組織では、従業員のセキュリティ意識を高め、新しい手順やツールに慣れるために、トレーニング内容を更新する必要もあります。
復旧の成功条件を実装する
システムとネットワークを復旧させて通常業務に戻す場合には、ビジネスで成功と定義される条件に対して合意を取り付けることが重要です。ネットワークセキュリティエンジニアは、修復が確実に成功していることを考慮して、システムを本番環境に戻せるタイミングを確認する必要があります。システムは、正常に機能していて、パッチが適用済みで、今後の脅威に対して強化されていなければなりません。
その他の考慮事項は次のとおりです。
- データが破壊または改ざんされている場合には、システムを信頼できるバックアップから復旧する必要があるかどうか。そうする場合には、どのバックアップを使用すべきか。
- 追加の監視の推奨と、追加の監視を使用すべき期間のタイムライン。
- 同様の攻撃を再発させないための追加のツールの特定。
- 実施された修復手順と復旧したシステムの現在の状態を関係者が理解できるようにするための、実行した復旧作業の概要の周知。
習得度チェック
では、これまでに学んだ内容を復習しておきましょう。この習得度チェックは簡単な自己診断テストで、採点対象ではありません。左側の機能を右側の対応するカテゴリにドラッグしてください。全項目を結び付けたら、[送信] をクリックして習得度をチェックします。最初からやり直すには [リセット] をクリックします。
まとめ
このトレイルでは、ネットワークセキュリティエンジニアの仕事の基本について学習しました。また、ネットワークセキュリティエンジニアが、セキュリティフレームワークを活用してネットワークのアセット、ユーザー、トポロジーを識別し、ネットワークセグメンテーションや代替コントロールといったさまざまなツールを使用してネットワークを防御する方法も確認しました。さらに、侵入が発生したときに検知する方法や、インシデントに対応し、インシデントから復旧するためにネットワークセキュリティエンジニアが意識すべき手順についても学習しました。これで、ネットワークセキュリティエンジニアが持つスキルのセンスを身に付け、セキュリティエンジニアの日々の仕事も理解できたことでしょう。サイバーセキュリティに関する詳しい情報に関心がある方は、Trailhead のサイバーセキュリティの学習ハブを確認してください。
リソース
- 外部サイト: CIS Critical Security Control 17: Incident Response and Management (インシデントの対応と管理)
- 外部サイト: CIS Critical Security Control 11: Data Recovery (CIS Critical Security Control 11: データ復旧)
- PDF: NIST: Computer Security Incident Handling Guide (コンピューターセキュリティインシデントの処理ガイド)
- PDF: NIST Framework for Improving Critical Infrastructure Cybersecurity (重要なインフラストラクチャのサイバーセキュリティを改善するための NIST フレームワーク)