Protect Against DOS and DDoS Attacks with AWS Shield
Learning Objectives
After completing this unit, you’ll be able to:
- Explain denial-of-service (DoS) attacks and their impact.
- Explain distributed denial-of-service (DDoS) attacks and their impact.
- Explain how AWS Shield mitigates these attacks.
- Differentiate between AWS Shield Standard and AWS Shield Advanced.
Think of a website as a library. Under normal operations, a library member can call ahead to place books on hold. A librarian then locates these books and gets them ready for pick-up.
However, today a prankster calls in multiple times to put books on hold but never picks them up. The librarian is busy getting these books and is unavailable to fulfill other people’s legitimate requests. The librarian attempts to stop the false requests by blocking the prankster’s phone number.
Just like the example above, when you host applications, websites, and other resources in the AWS Cloud, it’s important to keep them protected against malicious attacks that can take up too many resources and interrupt access for legitimate users.
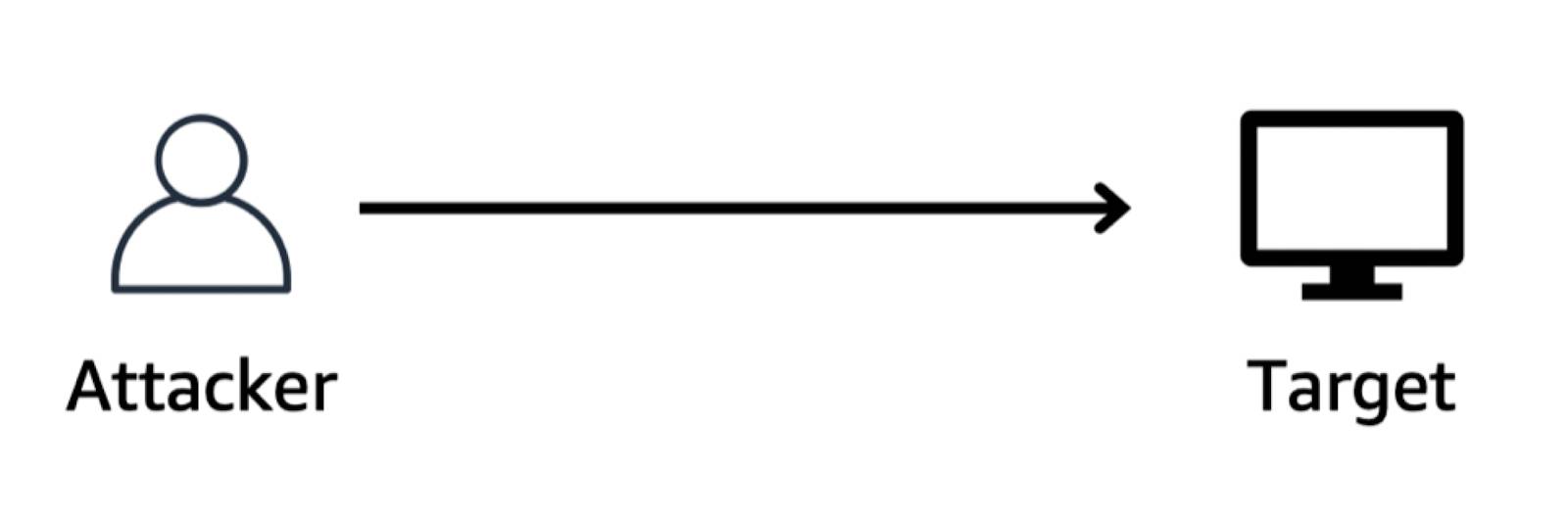
Denial-of-Service Attacks
A denial-of-service (DoS) attack is a deliberate attempt to make your website or application unavailable to users. Like the example where the prankster floods the library with false requests, an attacker floods your website or application with excessive network traffic until they’re overloaded and no longer able to respond. Simply put, if your resources are down, your users lose access.
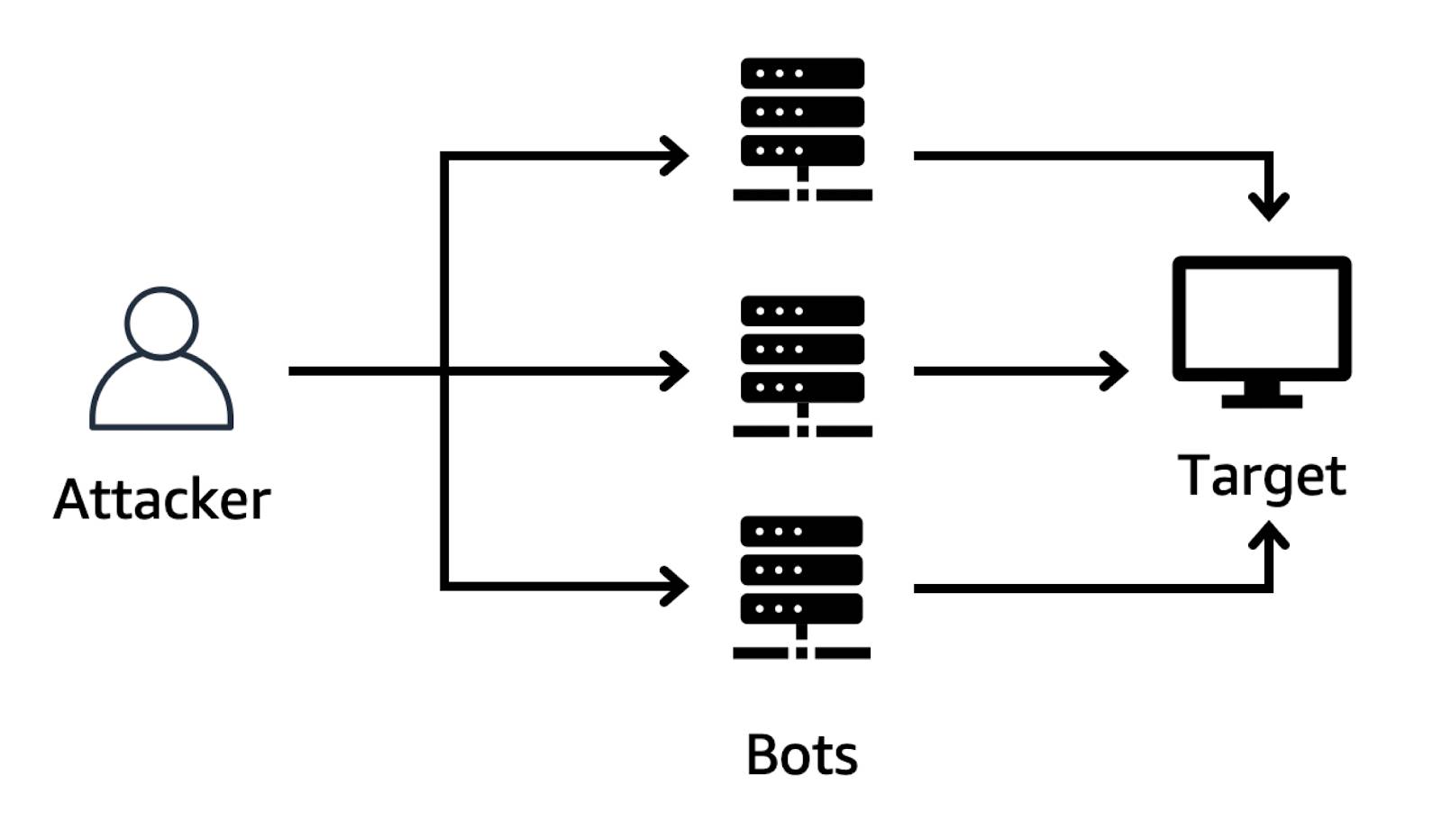
Distributed Denial-of-Service Attacks
Suppose the prankster from the library example enlists the help of some prankster friends. They all start calling in with requests to have books placed on hold, even though they do not intend to pick them up. These requests are coming in from different phone numbers, and it’s impossible for the library to detect and block them all in time. Additionally, the influx of calls has made it increasingly difficult for library members to get their calls through. This type of excessive resource consumption is exactly how a distributed denial-of-service (DDoS) attack works.
In a DDoS attack, multiple sources execute the same type of resource exhaustion attack against a target. This can come from a group of attackers, or even a single attacker using multiple infected devices to send excessive network traffic to an application or website.
AWS Shield

AWS Shield is a managed DDoS protection service that safeguards applications running on AWS. It comes in two tiers: Standard and Advanced.
AWS Shield Standard is automatically enabled for all AWS customers at no additional cost. It protects your AWS resources from the most frequently occurring network and transport layer DDoS attacks. The network layer decides which physical path the data takes, and the transport layer transmits data using transmission protocols such as TCP and UDP.
As network traffic comes into AWS for your applications and resources, AWS Shield Standard detects malicious traffic in real time and automatically applies mitigation to prevent attacks from occurring. For example, if AWS Shield Standard detects an unusually high traffic volume from different IP addresses for the same application, it checks for other anomalies and, if necessary, begins mitigating the traffic.
AWS Shield Advanced is a paid service that provides:
- Additional detection and mitigation against large and sophisticated DDoS attacks.
- Near real-time visibility into attacks.
- Integration with AWS Web Application Firewall (WAF).
Another benefit is its integration with Amazon CloudFront, a content delivery service. CloudFront distributes traffic across multiple edge locations and filters requests to ensure that only valid requests are forwarded to your applications and resources.
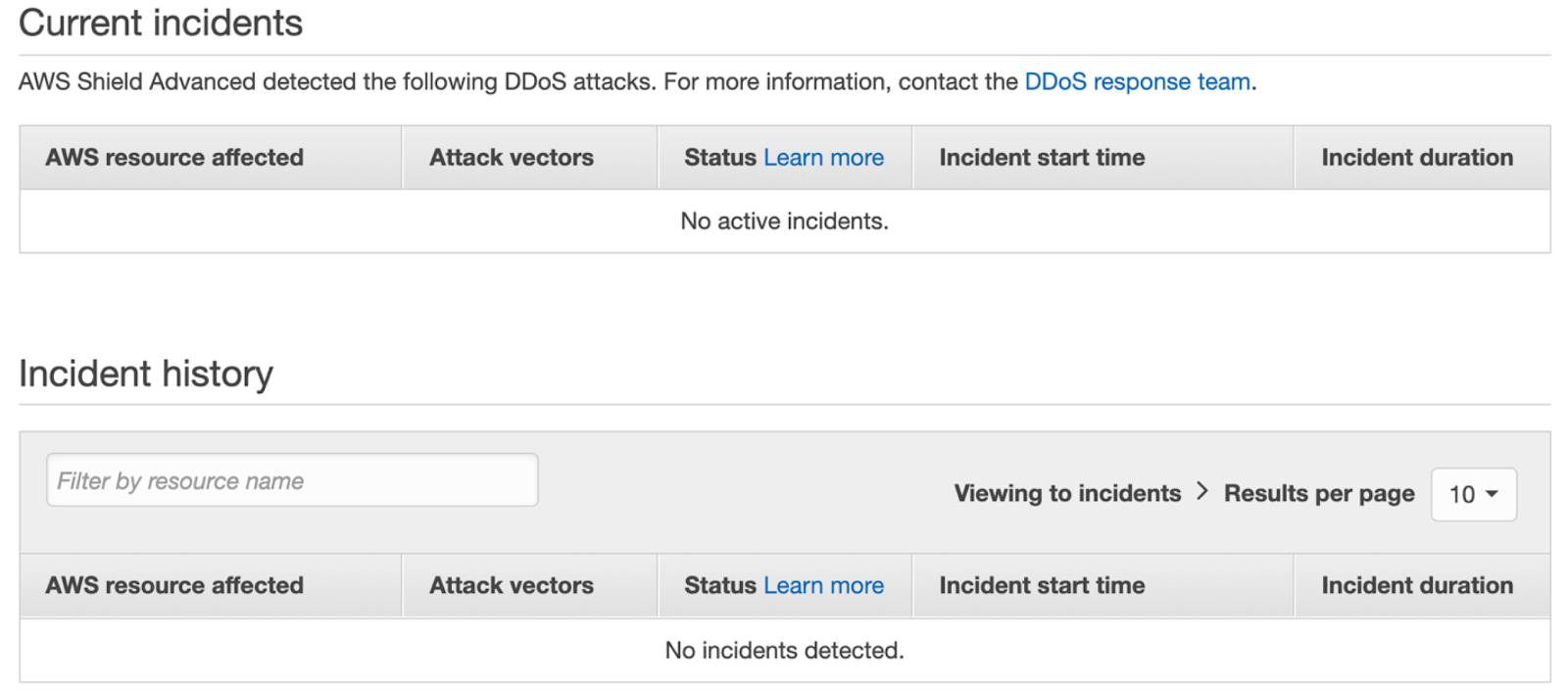
In AWS Shield, you can view details for any current incidents that have been detected on your AWS account’s resources and your account’s complete incident history. AWS Shield provides details on affected AWS resources, attack vectors involved in the incident, and the incident’s status, start time, and duration.
Know How to Protect Your AWS Resources
A key part of designing and scaling your cloud architecture is knowing how to protect it through implementing best practices for security. AWS Shield Standard and Advanced offer many features to protect your AWS resources against DDoS attacks, so that you can spend less time on manual security tasks and more time innovating for your customers.
In the next unit, you learn about AWS compliance services.