Learn About AWS Security Services
Learning Objectives
After completing this unit, you’ll be able to:
- Explain the features of Amazon Inspector.
- Explain the features of AWS Security Hub.
- Explain the features of AWS Web Application Firewall (WAF).
- Explain the features of AWS Key Management Service (KMS).
AWS offers a variety of security services to help you keep your data safe and secure in the cloud. You can also automate security tasks so you can spend less time managing security and more time innovating.
Amazon Inspector

Amazon Inspector is an automated security assessment service that helps improve the security and compliance of applications deployed on AWS. It checks for issues such as exposed resources and deviations from development best practices. It also helps save time.
Suppose that you have several Amazon EC2 instances, and you want to ensure that they’re all properly configured with the recommended password complexity settings. Instead of manually checking the settings for each EC2 instance, you can run a vulnerability assessment through Amazon Inspector, which scans all of the EC2 instances to check if the password complexity settings are compliant.
AWS Security Hub

How can you keep track of all your security statuses and findings across all the AWS services you’re using? Wouldn’t it be great if you had one place you could go to review your security checks?
Instead of constantly switching back and forth between separate tools, you can monitor all your security findings and compliance checks in AWS Security Hub. It aggregates, organizes, and prioritizes your security findings.
With AWS Security Hub, you can:
- Monitor all security findings and compliance checks in one place.
- Prioritize the actions that need to be taken on any security or compliance issues.
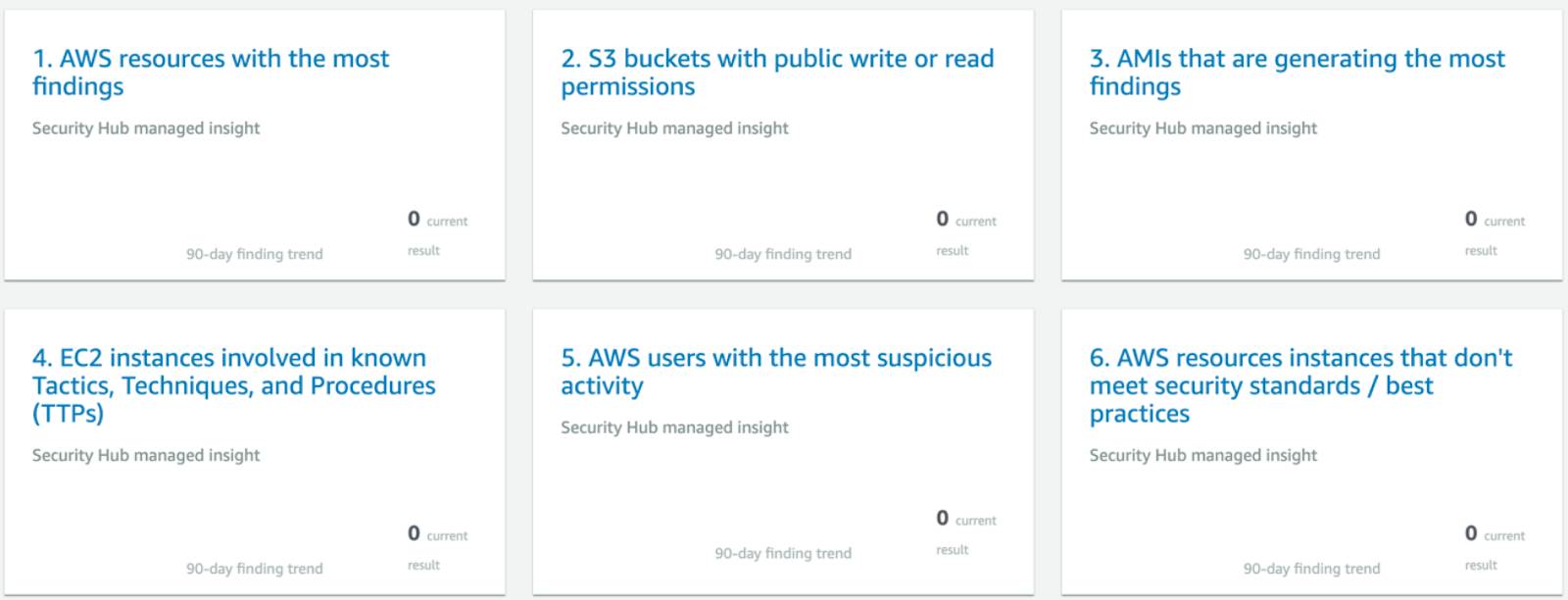
Review and Take Action with Security Hub Insights
The Insights area provides a quick glance into key areas across your AWS account where you might need to take action. Insights organizes findings into categories so you can easily prioritize which security issues to take on first. This includes:
- AWS resources with the most findings
- S3 buckets with public write or read permissions (and are therefore at risk of being accessed by anyone on the Internet)
- EC2 instances that have missing security patches for important vulnerabilities, and more
AWS Web Application Firewall (WAF)

AWS Web Application Firewall (WAF) is a service that helps to protect your web applications and APIs against common web exploits that may affect application availability, compromise security, or consume excessive resources.
With AWS WAF, you can control the network traffic that comes into your web applications by configuring security rules to protect against attacks or specific traffic patterns. Rules define how the firewall should inspect web requests and what to do when a request matches certain criteria.
Some examples of criteria that you can specify in AWS WAF are:
- IP addresses or address ranges that requests originate from
- Specific strings that appear in the request
- Scripts that are likely to be malicious
To save time, you can implement some of the AWS Managed Rules for AWS WAF. AWS Managed Rules are a set of AWS WAF rules curated and maintained by the AWS Threat Research Team. They are based on common Internet threats and are regularly updated by AWS as new security issues become known.
AWS Key Management Service (KMS)

AWS Key Management Service (KMS) enables you to create and control the encryption keys that are used to encrypt and protect your data.
When data is encrypted, the information within it is hidden so that it cannot be read without a secret key. With AWS KMS, you can control who can access your master encryption keys and gain access to your data.
AWS KMS is integrated with dozens of AWS services, including Amazon Simple Storage Service (S3), Amazon Relational Database Service (RDS), AWS Lambda, and more.
Wrap-Up
You can use AWS security services to protect your data and automate many of the tasks that you might have previously done manually. The integration across multiple AWS services helps you and your team stay on the same page when it comes to security alerts and remediation.
In the next unit, you learn about distributed denial-of-service (DDoS) attacks and how to use AWS Shield to keep your applications safe from them.