Learn About Connected Apps
Learning Objectives
- Describe what a connected app is.
- Describe how you can use a connected app.
- Identify the role you’ll play—developer or admin—with connected apps.
Begin Your Journey
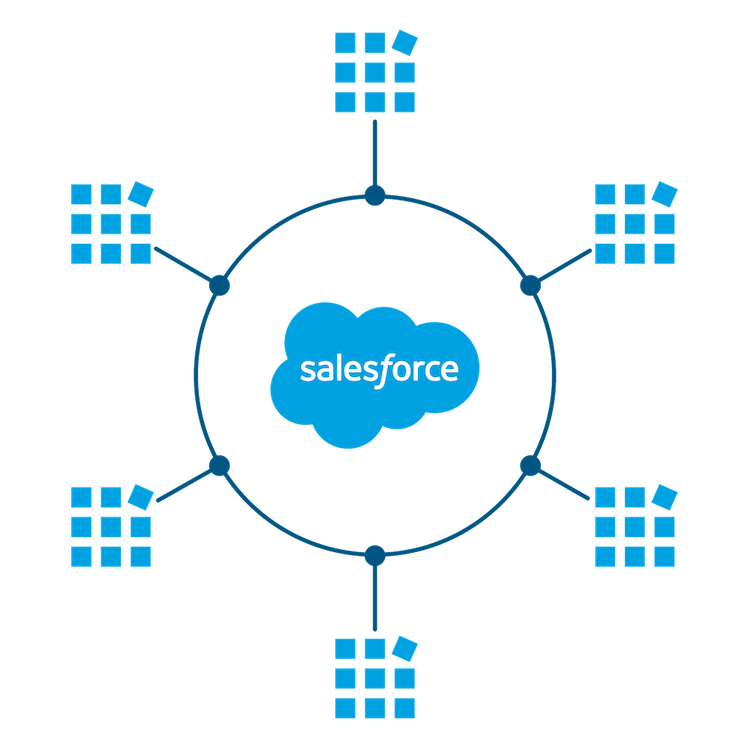
If you’re at all familiar with connected apps, you know that they can be used in a multitude of ways. And if you’re not familiar with connected apps, you’re about to learn that they are the framework to connect your users, external services, and Salesforce. The connected apps feature is a big one, and it takes a Trailhead trail to master. But don’t worry! We guide you along your journey, starting with the basics here.
In this module, we talk about how you can use connected apps. In future modules, we go into the details of creating and configuring connected apps. By the end of our journey, you’ll be a connected apps ace.
What’s a Connected App?
A connected app is a framework that enables an external application to integrate with Salesforce using APIs and standard protocols, such as Security Assertion Markup Language (SAML), OAuth, and OpenID Connect. Connected apps use these protocols to authorize, authenticate, and provide single sign-on (SSO) for external apps. The external apps that are integrated with Salesforce can run on the customer success platform, other platforms, devices, or SaaS subscriptions.
For example, when you log in to your Salesforce mobile app and see your data from your Salesforce org, you’re using a connected app.
By capturing metadata about an external app, a connected app tells Salesforce which protocol—SAML, OAuth, and OpenID Connect—the external app uses, and where the external app runs. Salesforce can then grant the external app access to its data, and attach policies that define access restrictions, such as when the app’s access expires. Salesforce can also audit connected app usage.
How Can My Salesforce Org Use Connected Apps?
There are several ways in which your org can benefit from using connected apps. Let’s introduce you to these use cases.
Access Data with API Integration
When developers or independent software vendors (ISV) build web-based or mobile applications that need to pull data from your Salesforce org, you can use connected apps as the clients to request this data. To do so, you create a connected app that integrates with Salesforce APIs.
For example, if you want to build a web-based app that pulls in order status from your Salesforce org, you can create a connected app for it. The connected app, with the help of OAuth 2.0, integrates the web-based app with your Salesforce API, giving it authorized access to the defined data.
Or maybe you want to build a mobile app that looks up customer contact information from your Salesforce org. You can use Salesforce Mobile SDK to implement OAuth 2.0 for your connected app. Your connected app integrates the mobile app with your Salesforce API, and gives it authorized access to the defined data.
Depending on the type of connected app that you’re integrating with the Salesforce API, you can choose from several OAuth 2.0 authorization flows. We talk about each of these flows in the next unit.
Integrate Service Providers with Salesforce
When Salesforce acts as your identity provider, you can use a connected app to integrate your service provider with your org. Depending on your org’s configuration, you can use one of these methods.
Use a connected app with SAML 2.0 to integrate a service provider with your org. Salesforce supports SAML single sign-on (SSO) when the service provider or the identity provider initiates the flow.
For example, you’ve built a custom Your Benefits web app that implements SAML 2.0 for user authentication. You want your users to be able to log in to this app with their Salesforce credentials. To set up this SSO flow, configure the Your Benefits web app as a connected app. Because your org implements the SAML protocol, your Salesforce org is already configured as the identity provider. Your users can now log in to the Your Benefits web app with their Salesforce credentials.
You can also use a connected app with OpenID Connect to integrate a service provider with your Salesforce org. To use this option, the service provider must accept OpenID Connect tokens.
For example, you want your users to sign on directly from your Salesforce org to an external Wellness Tracker app that accepts OpenID Connect. To set up this SSO flow, configure the Wellness Tracker app as a connected app with the OpenID Connect scope. This configuration enables the SSO flow for your Wellness Tracker app by integrating the service provider with your Salesforce org.
We go into more detail about these use cases in a later unit. In the meantime, you can read all about Salesforce Identity Connect and SSO in the Identity Basics Trailhead Module .
Provide Authorization for External API Gateways
Salesforce can act as an independent OAuth authorization server to protect resources hosted on an external API gateway. Using OpenID Connect dynamic client registration, resource servers can dynamically create client apps as connected apps in Salesforce. Salesforce can then authorize these connected apps to access protected resources hosted by the third-party service.
For example, Salesforce can act as the OAuth authorization server for API gateways that are hosted on MuleSoft's Anypoint Platform. MuleSoft’s Anypoint Platform, which is the resource server, can dynamically create client apps as connected apps. These connected apps can send a request to Salesforce asking for access to data protected by the API gateways. Salesforce can then authorize and authenticate the connected apps, granting them access to the data protected by the API gateways.
If this use case seems a bit complicated, don’t worry. We walk you through it in a later unit.
Manage Access to Third-Party Apps
If your org uses third-party apps, such as a third-party app from the AppExchange, admins can set security policies to control what data the third-party app can access from your org. Admins can also define who can use the third-party app.
For example, you install a third-party app that allows your org’s users to make travel reservations. By selecting the option “Admin approved users are pre-authorized” for the connected app, you can assign specific user profiles to the app. Only the users with this user profile can access the app. You can also set a refresh token policy to revoke the travel reservation app’s access to your Salesforce data after a set amount of time.
In addition to setting security policies to manage third-party apps, you can uninstall, and—when necessary—block these apps from the Salesforce org.
We go over this use case in a future module about managing connected apps.
What Role Do I Play with Connected Apps?
To put it simply, developers create and configure authorization flows for connected apps, and admins set policies and permissions to control connected app usage. But there’s much more to each role.
Connected App Developer
A connected app developer is a Salesforce developer or ISV who builds API integrations or external apps that can access Salesforce data as a connected app. As a developer, you can build a connected app for your org, but other Salesforce orgs can install and use it too.
Connected App Admin
As a connected app admin, you install, uninstall, and—when necessary—block connected apps from the Salesforce org. You also configure permissions and policies for the apps, explicitly defining who can use the connected apps and where they can access the apps from. These permissions and policies, which include profiles, permission sets, IP range restrictions, and multi-factor authentication, provide extra security for your org.
What’s Next
We’ve given you an overview about how to use connected apps. Now that we’ve introduced you, let’s get to know each use case a little better, starting with how you can use connected apps to access data.
Resources
- Salesforce Help: Connected Apps
- Trailhead module: Identity Basics
- Salesforce Developers website: Identity Developer Center