Access Data with API Integration
Learning Objectives
- Describe how OAuth 2.0 enables API integration for connected apps.
- Identify the API integration use cases for connected apps.
OAuth 2.0 Authorization Flow for Connected Apps
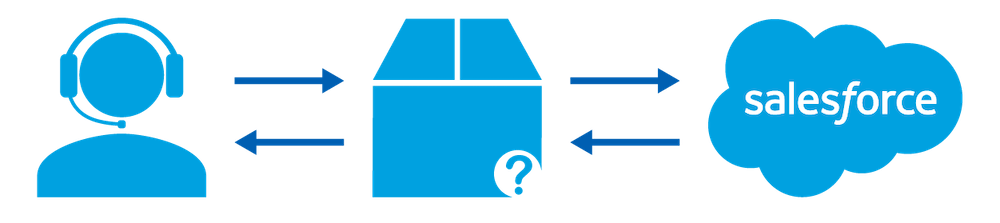
You can use a connected app to request access to Salesforce data on the behalf of an external application. For a connected app to request access, it needs to be integrated with the Salesforce API using the OAuth 2.0 protocol. OAuth 2.0 is an open protocol that enables authorization and secure data sharing between applications through the exchange of tokens. When developers want to integrate their app with Salesforce, they use OAuth APIs. These OAuth APIs enable a user to work in one app but see the data from another.
When you open the Salesforce mobile app to access your Salesforce data, you’re initiating an OAuth 2.0 authorization flow. In this flow, your Salesforce org is the resource server and the Salesforce mobile app is the client requesting access. You authorize the Salesforce mobile app to access and manage your Salesforce data over the web at any time.

The flow of events during OAuth authorization depends on the state of authentication on the device.
First Time Authorization Flow
- You open the Salesforce mobile app.
- An authentication prompt appears.
- You enter your username and password.
- The Salesforce mobile app sends your credentials to Salesforce and initiates the OAuth authorization flow.
- You approve the request to grant access to the Salesforce mobile app, as shown in the image above.
- Salesforce sends the mobile app access and refresh tokens as confirmation of successful authorization.
- The Salesforce mobile app starts.
Ongoing Authorization
- You open the Salesforce mobile app.
- If the session is active, the Salesforce mobile app starts immediately. If the session is stale, the Salesforce mobile app uses the refresh token from its initial authorization to get an updated session.
- The Salesforce mobile app starts.
Web App Integration (OAuth 2.0 Web Server Flow)
To integrate an external web application with the Salesforce API, use the OAuth 2.0 web server flow. With this flow, the server hosting the web app must be able to protect the connected app’s identity, defined by the client ID and client secret.
For example, you’ve recently developed a website that allows secure access to customer order status. The order status data is securely stored in your Salesforce CRM platform. To authorize Help Desk users to view a customer’s order status, you develop an Order Status app and configure it as a connected app with the web server flow.
- A Help Desk user clicks the Order Status web app.
- The connected app directs the user to Salesforce to authenticate and authorize the app to access the order status data.
- The user approves the Order Status app to access the data.
- Salesforce sends a callback to the Order Status app with an authorization code.
- The Order Status app passes the authorization code to the Salesforce token endpoint, requesting an access token.
- Salesforce validates the authorization code, and sends back an access token that includes associated permissions in the form of scopes.
- The Order Status app sends a request back to Salesforce to access the order status data. Its request includes the access token with the associated scopes.
- Salesforce validates the access token and associated scopes.
- The Order Status app can access the protected data, and the customer’s order status is displayed in the app.
Mobile App Integration (OAuth 2.0 User-Agent Flow)
A connected app is a primary means by which a mobile app connects to Salesforce. Although not required, you can use Salesforce Mobile SDK to build mobile applications as connected apps. These apps can access Salesforce OAuth services and call Salesforce REST APIs.
Let’s say you use Salesforce Mobile SDK to build a mobile app that looks up customer contact information from your Salesforce org. Mobile SDK implements the OAuth 2.0 user-agent flow for your connected app, integrating the mobile app with your Salesforce API and giving it authorized access to the defined data.
- The end user opens the mobile app.
- The connected app directs the user to Salesforce to authenticate and authorize the mobile app.
- The user approves access for this authorization flow.
- The app receives the callback from Salesforce to the redirect URL, which extracts the access and refresh tokens.
- The connected app uses the access token to access data on the end user’s behalf.
For more information about Salesforce Mobile SDK, check out the Salesforce Mobile SDK Basics Trailhead Module.
Server-to-Server Integration (OAuth 2.0 JWT Bearer Flow)
In some cases, you need to authorize servers without interactively logging in each time the servers need to exchange information.
To provide authorization for server-to-server integration, you can use the OAuth 2.0 JSON Web Token (JWT) bearer flow. This flow requires prior approval of the client app.
- The report service begins its nightly batch report.
- The connected app sends the JWT, which enables identity and security information to be shared across security domains, to the Salesforce token endpoint.
- Salesforce validates the JWT based on a signature using a previously configured certificate and additional parameters.
- Assuming that the JWT is valid and that the connected app has prior approval, Salesforce issues an access token. Prior approval happens in one of these ways.
- If your connected app policy is set to “Admin approved users are pre-authorized,” you can use profiles and permission sets.
- If your connected app policy is set to “All users may self-authorize,” you can use end-user approval and issuance of a refresh token. However, the client doesn’t need a current or stored refresh token. The client also doesn’t need to pass a client secret to the token endpoint.
- The connected app uses the access token to access the protected data on the Salesforce server.
- The report service pulls the authorized data into its nightly report.
IoT Integration (OAuth 2.0 Device Flow)
To integrate devices with limited input or display capabilities, such as Smart TVs, you can configure connected apps with the OAuth 2.0 device flow.
With the device flow, end users can authorize connected apps to access Salesforce data using a web-based browser.
For example, a customer uses your bluetooth device to control their house lights while they are away for the evening. You can create a connected app for the bluetooth device to enable this flow.

- The user opens the bluetooth app on their mobile device and clicks Turn On Lights.
- The connected app posts a request to the Salesforce authorization endpoint.
- Salesforce verifies the request and returns a human-readable user code, verification URL, and device code.
- The bluetooth app displays the device code, and instructs the user to enter it at the specified verification URL. The app also begins polling the Salesforce token endpoint for authorization.
- The user clicks the link to the verification URL and enters the code.
- The user then authorizes the app to access their protected data, in this case their home’s location.
- Salesforce sends an access and refresh token to the connected app.
- The bluetooth app can access the user’s home location and turn on the lights.
You can also use the asset token flow for IoT integration. This flow uses a JWT that ties the user and device together, authorizing the device. You can read more about this flow in this Salesforce Help article: OAuth 2.0 Asset Token Flow for Securing Connected Devices.
Other OAuth API Integration Flows
In addition to the examples above, you can also use the following OAuth 2.0 flows with connected apps.
Refresh Token Flow
As part of the web server and user-agent flows, a connected app can use a refresh token to request a new access token after the current access token expires. This flow is particularly helpful when you don’t want user intervention after an app is authorized.
Client Credentials Flow
When you want to directly share information between two applications without requiring user interaction, you can use the OAuth 2.0 client credentials flow. In this flow, the client app exchanges its client credentials defined in the connected app—its consumer key and consumer secret—for an access token. This flow eliminates the need for explicit user interaction, though it does require you to specify an integration user to run the integration. You can use this flow as a more secure alternative to the OAuth 2.0 username-password flow.
SAML Bearer Assertion Flow
A connected app can use a SAML assertion to request an OAuth access token to call Salesforce APIs.
SAML Assertion Flow
This flow provides an alternative for orgs that are currently using SAML to access Salesforce and want to access the web services API in the same way.
Moving On
Now that you’ve learned more about when to use connected apps for accessing data in your Salesforce org, let’s move on to using connected apps for single sign-on.
Resources
- Trailhead module: Identity Basics
- Salesforce Help: OAuth Authorization Flows
- Salesforce Help: Authorize Apps with OAuth Flows
