Educate Your Users to Help Protect Your Org
Learning Objectives
After completing this unit, you’ll be able to:
- Explain a strong password policy.
- Describe how to avoid falling victim to phishing emails.
- Define the least privilege approach to user permissions.
Users Have Access to Valuable Data
As we covered in the previous unit, today’s cybercrime target is more often than not an employee. Employees who have access to sensitive data, like financial records or healthcare data, are valuable targets for hackers. That's why educating your Salesforce users about secure behavior can go a long way toward securing your implementation and keeping your customers' data secure.
An individual user plays a critical role in keeping your data secure. Educating users about their role in keeping Salesforce data secure will pay dividends in the long run. The most valuable asset a company can possess is customer trust. And, it is your responsibility to keep their data safe in order to earn their trust every day.
Talk to your colleagues or other Salesforce Administrators about creative ways they have worked with their users to make them more aware and motivated to do their part to keep data secure. Finding fun ways to educate users on security, like hosting competitions or games to see who can register for multi-factor authentication (MFA) the quickest, will make users more open to adopting secure behaviors. You can also take a more systematic approach and partner with your IT or Cybersecurity teams to conduct regular phishing tests that train users to stay vigilant against phishing emails from hackers.
Pay Attention to Passwords
Passwords are your first line of defense against unauthorized access to your Salesforce implementation. At minimum, set password history, length, and complexity requirements to enhance password security and specify what to do if users forget their password.
To increase protection of user accounts, we also require customers to use MFA to access Salesforce. MFA means you must have multiple forms of authentication to gain access, usually something you know, like a password, and something you have, like a code on a mobile authenticator app.
The National Institute of Standards and Technology (NIST) publishes guidelines for digital identity authentication and lifecycle management regularly. These simple best practices help reduce password threats, whether or not you’re using additional technologies like MFA and single sign-on (SSO) for extra protection.
Use unique passwords
We've all done it — used the same password for multiple websites (Rover123 anyone?). While this makes for a password that is easy to remember, because the schema is so common, adding minor variations is the first thing attackers try when attempting to crack a password. Using insecure passwords like this is a common way for attackers to access important information when a website or platform becomes compromised (hacked), and user credentials are made publicly available or sold online. If the password used for the compromised website is also used for something important, like your online banking, or corporate database access, this can cause serious problems. If you use the same password with even minor variations, attackers can gain access to many sites by simply trying out variations.
Use complex passwords
Require passwords to be at least 10 characters — but longer passwords are even better. Encourage users to create a passphrase (a set of actual words strung together) to make it easier to remember, combined with at least one number and one character. An example of a strong password would be: "CouchEagle$Window9783Fan."
Change passwords annually
Require users to reset their passwords on an annual basis.
Keep passwords to yourself
Remind your users never to share a password, including their Salesforce password, with anyone, either online or over the phone.
Use a Password Manager
Using a password manager, like LastPass or 1Password, is one of the best ways to keep your passwords strong and secure. Your organization may provide a password manager for you, but if they do not, you can still choose one for yourself. Password managers allow you to save login information for any website, generate secure passwords, and store them in a secure database without requiring you to memorize complex, strong passwords for every service you use. We also recommend enabling MFA for your password manager to make it extra secure.
Salesforce will never contact you or your users over email or phone asking for your password. If someone contacts you posing as Salesforce and requests a password or any other sensitive information (for example, social security number), immediately report the incident to security@salesforce.com.
Don't Get Fooled by Phishing
Most phishing attacks use malware (malicious software) to infect a computer with code designed to steal passwords or data or to disrupt an entire computer or network. Fortunately, you and your users don’t need to be security experts to spot a phishing email.
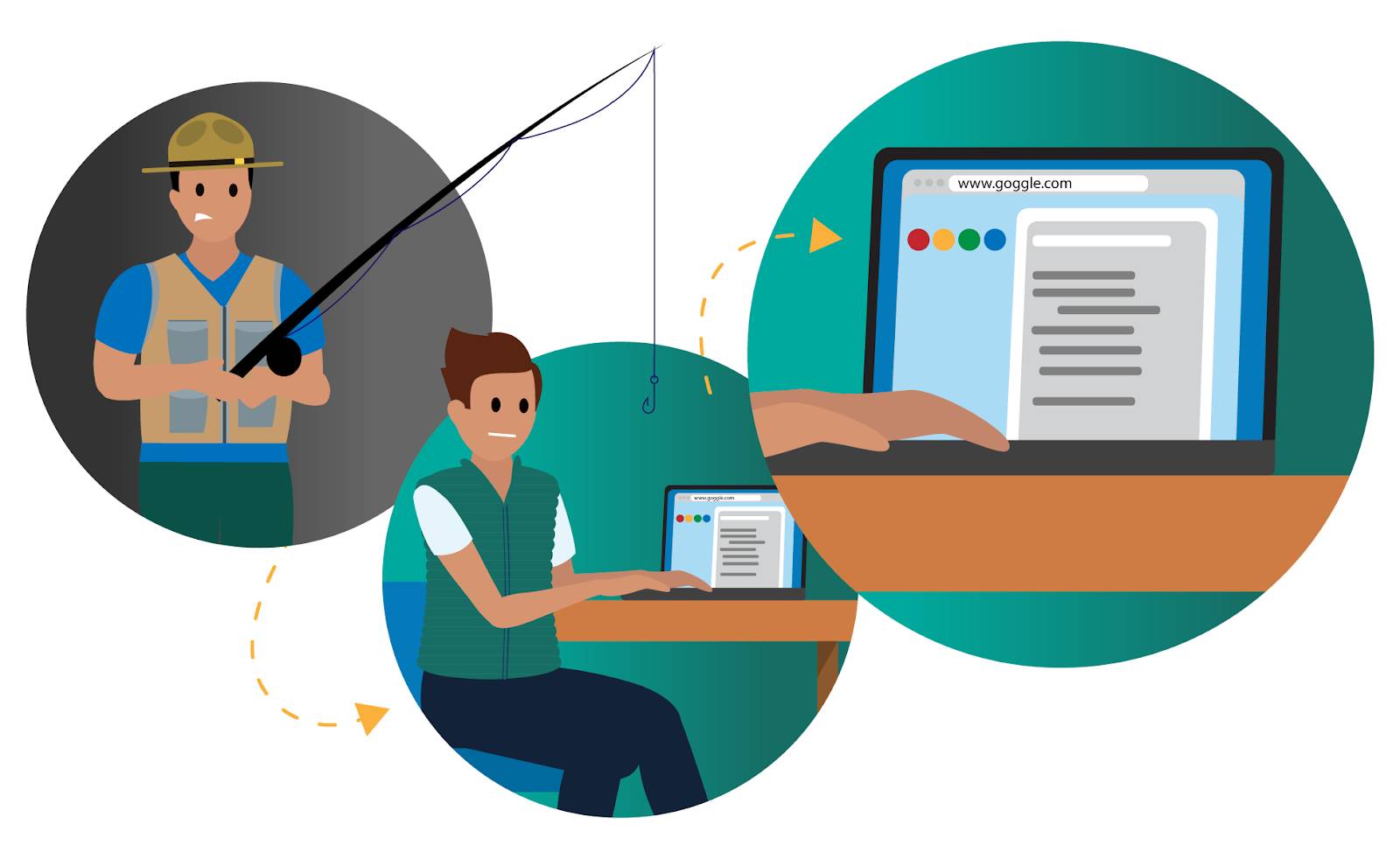
Look up the subject or sender's email using a search engine
Remember that phishing emails are designed to exploit normal human behavior and lure you into clicking a malicious link or downloading an attachment. They can be very believable and based on a legitimate premise, like stating that a package is being delivered to you or that your paycheck is ready. Often, the sender’s email address can raise red flags because it doesn’t match the actual sender’s company name. If you aren’t sure if an email is legitimate, try typing the subject line or the sender's email address into a search engine and see if any other sources have reported it to be a phishing attempt.
Consider the source and verify links before clicking
Never click a link or open an attachment in a suspicious-looking email, or an email from an unknown sender. Instruct your users to pause and really assess an email from an unknown sender before they click. Another good trick to verify that the links inside the email are legitimate is to hover over them to validate where they are being directed. For example, if an email asks you to click on a link to a marketing whitepaper from Salesforce, hover over the link to see if the URL ends in salesforce.com.
Check with Salesforce
If you’re not sure about whether an email is from Salesforce, alert your company’s IT or cybersecurity team. Because the security team will need the email headers, it's important that you forward a copy of the suspicious email as an attachment to security@salesforce.com. Please include the words "phish" or "malware" in the subject line to indicate that the email is a suspected phishing email.
Your company's security team likely works closely with the Salesforce Security team to identify malicious emails. You can also check security.salesforce.com for a listing of recent email threats that the Salesforce Security team is aware of.
Involve Your Users in Security
Small changes in user behavior can have a major impact. When the Salesforce Security team sends phishing emails to our own employees, we’ve learned that people who’ve taken our security training are only half as likely to click on phishing links, and almost twice as likely to report them, compared to employees who haven’t been trained. Consider running phishing tests at your own company, and regularly remind users to follow security best practices
Dole Out Rights Sparingly
A key security practice is to provide users with the minimum access they need to do their job, otherwise known as the principle of least privilege.
For example, a business analyst doesn’t need to see billing information for customers. A strong best practice is to limit the number of users with admin rights (generally we recommend no more than five), and check periodically to make sure that those same individuals need to continue to have administrator permissions. You can also limit visibility and permissions at the field level. With time, who needs what access can change so it’s important to have a mechanism in place to double-check access privileges regularly.
Resources
- Salesforce Blog: Be a Security-Minded Admin
- External Site: NIST Special Publication 800-63B: Digital Identity Guidelines
- Trailhead: User Authentication
- Salesforce Security: Salesforce Security Resources