User Authentication Troubleshooting Superbadge Unit
Troubleshoot user authentication issues based on a scenario.
User Authentication Troubleshooting Superbadge Unit
What You'll Be Doing to Earn This Superbadge
- Help a new user connect to the Salesforce Authenticator app.
- Troubleshoot single sign-on configuration.
- Take security precautions after a user’s phone is stolen.
Concepts Tested in This Superbadge
- User Authentication
Prework and Notes
Sign Up for a Developer Edition Org with Special Configuration
To complete this superbadge unit, you need a special Developer Edition org that contains special configuration and sample data. Note that this Developer Edition org is designed to work with the challenges in this superbadge unit.
-
Sign up for a free Developer Edition org with special configuration.
Fill out the form. For Email address, enter an active email address.
- After you fill out the form, click Sign me up.
When you receive the activation email (this might take a few minutes), open it and click Verify Account.
Complete your registration by setting your password and challenge question. Tip: Save your username, password, and login URL in a secure place—such as a password manager—for easy access later.
You are logged in to your superbadge Developer Edition org.
Now, connect your new Developer Edition org to Trailhead.
Make sure you’re logged in to your Trailhead account.
In the Challenge section at the bottom of this page, select Connect Org from the picklist.
On the login screen, enter the username and password for the Developer Edition org you just set up.
On the Allow Access? page, click Allow.
On the Want to connect this org for hands-on challenges? page, click Yes! Save it. You are redirected back to the Challenge page and ready to use your new Developer Edition org to earn this superbadge.
Now that you have a Salesforce org with special configuration for this superbadge unit, you’re good to go.
Use Case
As a Salesforce administrator at Cloudy With a Chance of Finance, your team is in charge of all things related to user authentication. In addition to your other admin duties, you generally spend part of each day working with new users or troubleshooting authentication issues that arise.
In this superbadge unit, you work through a day in the life of an #AwesomeAdmin as you solve some user authentication cases.
Note: In this superbadge unit, you need to log in as other users and have to log back in as your admin user before you make additional configurations. Make note of your username and password or use the Launch button above the challenges to log in again as the admin user.
Monday, 9 AM: The Case of the New User
Sally Wu is new to the Cloudy with a Chance of Finance organization and is working through all of her new employee onboarding tasks. She’s having trouble adding a verification method for the org’s multi-factor authentication (MFA) requirement and has asked for your assistance.
With Sally (figuratively) at your side, log in as her user to walk her through the steps to connect the Salesforce Authenticator app and log in to the Cloudy org.
Note: You need to pretend your mobile device is Sally’s in this scenario and change her user email address to yours. If you already have the Salesforce Authenticator app installed on your device, you can simply add Sally’s account.
Monday, 11 AM: The Case of the Broken Single Sign-On Configuration
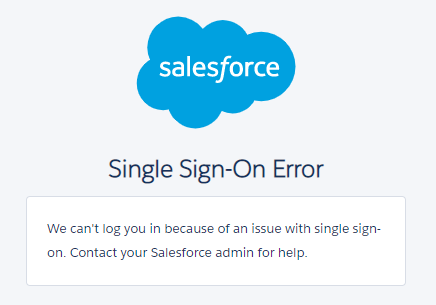
Gabriel, your coworker on the Admin team, is having trouble configuring single sign-on (SSO) and has asked for your expertise. The goal of the SSO implementation is to require a group of users to log in to various applications and other Salesforce orgs using their Federation ID.
Gabriel has configured the SAML Single Sign-On Settings in the Cloudy Salesforce org. However, when he uses the Axiom Identity Provider (IdP) to generate a SAML Response with his test user, Malcolm Doerr, he gets the following error.
The following is what he entered in the Axiom IdP. If it’s not specified, he left it blank or kept the default setting.
| SAML Version | 2.0 |
|---|---|
| Username OR Federated ID | <Malcolm Doerr’s Federation ID> |
| Issuer | https://axiomsso.herokuapp.com |
| Recipient URL | <Cloudy’s login URL endpoint> |
| Entity ID | https://trailhead.salesforce.com/ |
Note: Values listed in <angle brackets> are custom to your special org for this superbadge unit.
Take a look at Gabriel’s configurations and test using Malcolm Doerr’s user to see if you can figure out what’s causing the login attempt to fail. Once you’ve successfully logged in through the Axiom IdP as Malcolm, you can hand the project back over to Gabriel. Tip: Use an Incognito browser when logging in as Malcolm. Otherwise, be sure to log out and reauthenticate as your admin user before you make additional configurations.
Monday, 2 PM: The Case of the Stolen Phone
Sally Wu’s first day at Cloudy with a Chance of Finance was going great until she realized she forgot her phone at the lunch restaurant. She returned to look for it, but it wasn’t at the table and no one had turned a phone in to the restaurant staff. At 2 PM, she contacts your team.
Hi Admin team, I’m afraid my phone has been stolen (lucky first day, right?) and my manager told me to let your team know right away. Also, I’m embarrassed to admit this since your security training was very clear, but I recorded my Salesforce password in my phone’s notes app so my password may have been breached as well.
On a positive note, I’ve already generated my first lead! Is there a way I can log in to Salesforce without the Salesforce Authenticator app? I should have my new phone by tomorrow. Thanks for your help!
This is certainly not an ideal situation, but, as an experienced admin, you know exactly what to do! Make sure that potential bad actors are unable to log in with Sally’s current password or the Salesforce Authenticator app installed on her phone. Once you’re confident the org is secure, allow Sally an alternate option to verify her identity. Since she only needs this alternate verification option temporarily, make sure it’s only available for 8 hours.


