Learn About Bug Bounty Programs
Learning Objectives
After completing this unit, you’ll be able to:
- Define a bug bounty program.
- List the goals of a bug bounty program.
Bug Bounty Programs and Software Security
You’re in charge of security for your building. Do you simply lock the front door at the end of the day, leaving other doors and windows open? Of course not. You want to secure all access points. Today, organizations have to secure their software just as diligently as they do their physical spaces.
Identifying vulnerabilities is key to software security for organizations. Industry research shows the cost of identifying and fixing vulnerabilities early in the software development lifecycle is less expensive than responding to an incident later that was caused by bad actors exploiting the vulnerability.
Most companies have security processes in place for receiving vulnerability reports. A bug bounty program goes further. It provides valuable insight into the evolving threat landscape to help organizations enhance their preventative security efforts from the inside out. It does this by offering financial rewards for unknown vulnerabilities reported from outside the organization that meet the program guidelines. Let’s learn more by exploring the details of a Bug Bounty Program.
What Is a Bug Bounty Program?
A bug bounty program (BBP) is a way to crowdsource the discovery of software vulnerabilities, or bugs, by offering financial rewards to participants who proactively test eligible, in-scope products. Industry security researchers, known as ethical hackers, earn a bounty when they uncover a valid, unknown bug and safely and successfully submit it to the organization or entity. The organization is made aware of these vulnerabilities and can mitigate them before a malicious hacker exploits them.
The BBP helps an organization secure its software and keep “zero-days” off the illegal market.
Zero-day is an industry term for a specific type of vulnerability in software. A zero-day is new, unknown to the software vendor. And it can be easily exploited to adversely affect programs, data, networks, and stakeholders.
The term, zero-day (also written as 0-day), is often used in two ways in the context of the software industry.
- A zero-day vulnerability represents the vulnerability and the number of days a vendor has to mitigate it.
- The malicious use of the vulnerability is known as a zero-day exploit.
Both meanings are often shortened to zero-day and used interchangeably. The important takeaway is that a zero-day is always unwanted!
Large organizations have security teams who are tasked with making products and technology more secure. Security teams own both offensive and defensive security strategies for their products, which includes discovering and fixing issues before malicious actors find them. So why would they enlist outside security researchers to help? Let’s find out.
Purpose of a Bug Bounty Program
Why is a bug bounty program an integral part of so many companies’ security ecosystems? Let’s explore the typical benefits of a BBP.
- Expanded security capabilities
- Added perspectives
- Focused scope
- Increased Customer Trust
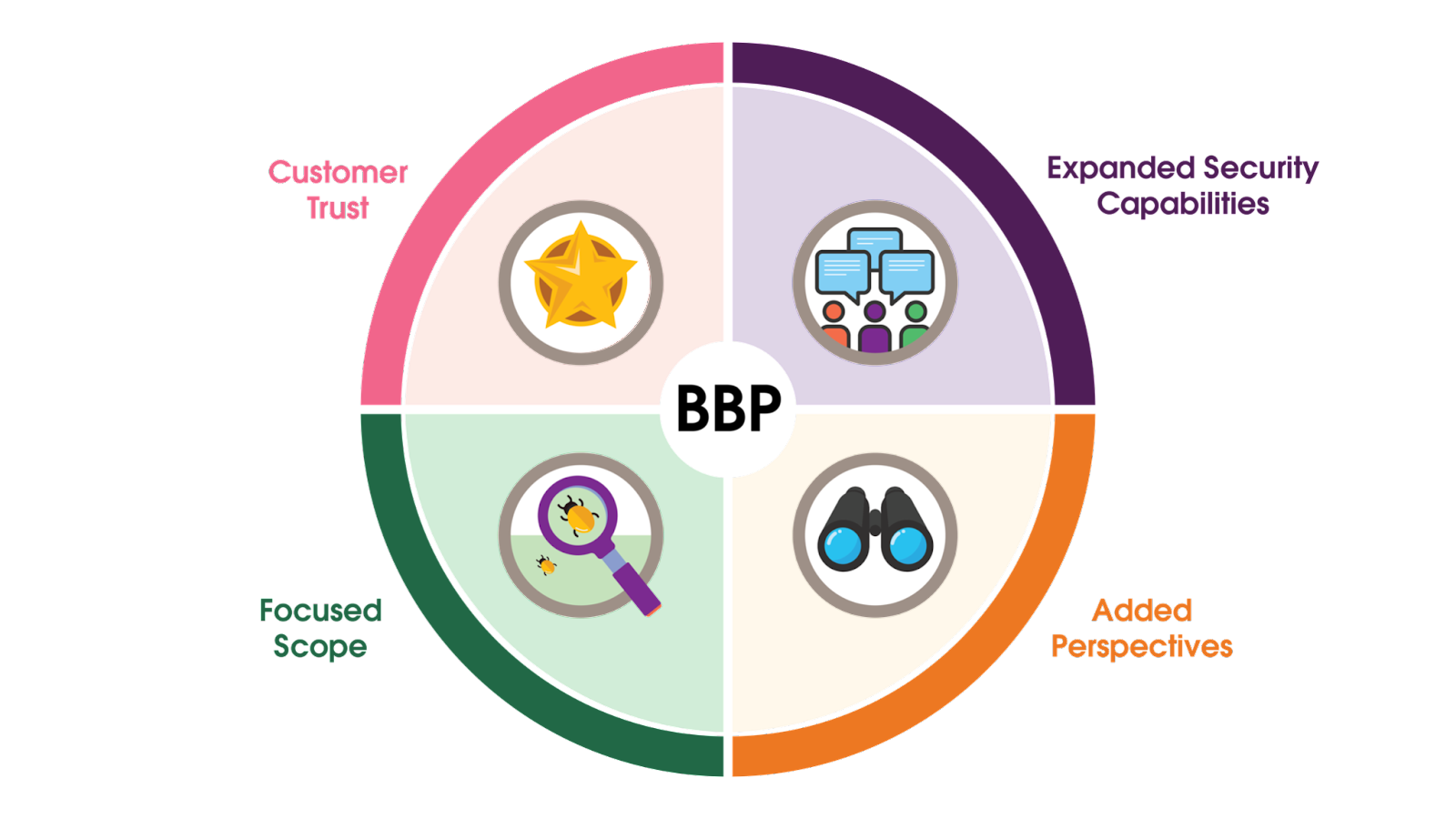
Expanded Security Capabilities
An organization that implements a bug bounty program increases its security force. The in-house security team augments its effectiveness by enlisting the skills and expertise of a diverse group of experts from outside the organization. In fact, a BBP can act as a force multiplier, increasing the numbers of the security team working to proactively fortify the organization’s defenses.
Increased Customer Trust
A bug bounty program can also improve an organization’s reputation for the delivery and maintenance of safe, secure products and services. It demonstrates an organization’s transparency and acknowledges that even with a world-class security team, vulnerabilities may occur. A BBP enlists the best security minds globally to security test an organization’s in-scope products, and signals to stakeholders that the organization maintains a high-functioning, mature security program.
Focused Scope
A bug bounty program can focus on specific products or assets. An example would be to target research on beta assets before a major update or new release. Security and product teams can also strengthen security when they offer products for testing in a controlled environment or a particular stage of development. Naturally, the more assets included in the program’s scope, the more value the program can provide to the organization.
Added Perspectives
Working with outside researchers, security teams get to see approaches to security that are different from an “insider” view. Reports from users in the field who probe from different angles will provide richer insights. External researchers have varying tactics, which can enable security teams to learn new strategies for better protecting their software.
It’s now clear why an organization adds a bug bounty program to an already-established security strategy. Next up, let’s look at how a BBP works: Its structure, work process, and personnel.
Resources
- Blog Post: What Is a Bug Bounty Program?
- Blog Post: How much do bugs cost to fix during each phase of the SDLC?
- External Site: Cybersecurity & Infrastructure Security Agency (CISA)