Manage Administrator Credentials
Learning Objectives
After completing this unit, you’ll be able to:
- Define privileged access management systems.
- Explain the principle of least privilege.
Privileged Access Management
While password managers are terrific for generating and securing your personal passwords, you need a more secure system for protecting the credentials of your privileged users (also known as administrative users). Privileged credentials are a subset of credentials (such as passwords) that provide elevated access and permissions across accounts, applications, and systems. Privileged passwords can be associated with humans, applications, service accounts, and more.
Privileged access management (PAM) solutions provide a way to store secrets, such as passwords and cryptographic keys (a word, number, or phrase that works in combination with an algorithm to encrypt [or scramble] plaintext). PAM solutions use a central tool to manage, delegate, and audit privileged access. PAM helps organizations implement least privilege, which is the principle that users receive only the necessary level of access to do their jobs.
Privileged Account Password Policy
To protect your systems your organization should develop and enforce a clear policy for privileged account passwords and share it with all relevant parties who use and manage these accounts.
It’s a good idea for organizations to develop privileged account password policies for both accounts accessed by people, and accounts accessed by other systems. These policies should include the mandatory use of long passphrases and multi-factor authentication (MFA) for human accounts.
Passwords rotation standards can ensure the systematic rotation of passwords for every account, system, networked hardware device, application, and service. Your rotation standards should include automatic notification to stakeholders when it's time to update passwords.
Implement Least Privilege
Defending your perimeters is not enough for security and data protection. Over and over again we see data breaches in both government and private sector systems that happen because network credentials are breached. Attackers in these cases are seeking to gain access to privileged accounts so they can gain access to sensitive data and private records.
When setting up administration credentials, think about implementing the principle of least privilege (POLP). We talk about POLP so often in security training because it is one of the fundamental means by which we can secure our systems. To review, the principle of least privilege is an IT security design principle that restricts access rights and program privileges to only those necessary for the required job. It’s the difference between having a key that works on every door, and one that only opens certain rooms.
One aspect of implementing least privilege is that you remove full local administrator access to system endpoints. For example, a user account that needs permission only for creating backups does not need the ability to install software, so that account has rights only to run backup and backup-related applications. Any other privileges, such as installing new software, should be blocked.
To make privileged management easier, it’s a good idea to automate granting least privilege based on who the user is, what they’re requesting access to, and the context of the request. Users should be able to access only the systems they need to do their jobs, and should not be granted general access to information.
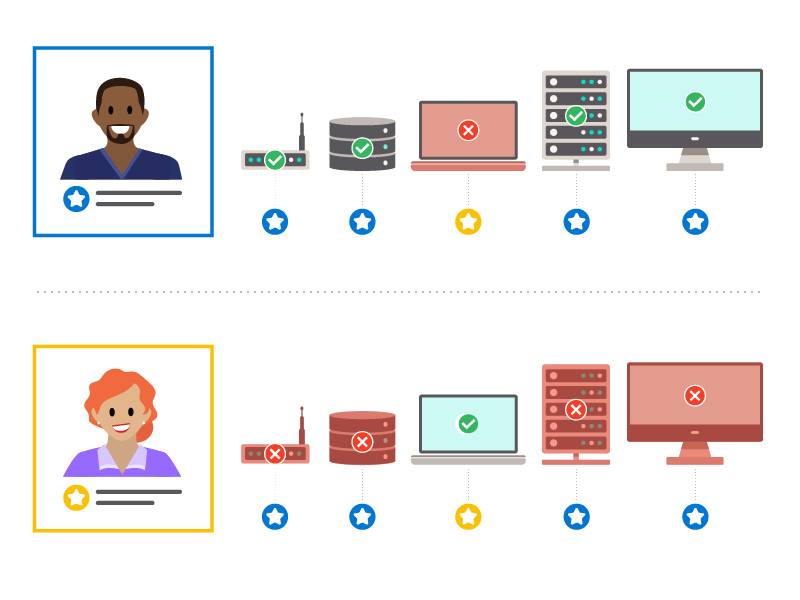
This means that Sally in Human Resources (HR), for example, should not be able to access the database of Bilal in Finance who is making global deals. Good privileged access management means that Sally has access to all the HR records she needs to do her job, and Bilal has access to all the financial records he needs to do his, but they do not have access to each other's files.
Choose a Privileged Access Management (PAM) Solution
Numerous PAM solutions are out there that provide various features and deployment options. You can test and evaluate a few before deciding which to implement. An important factor of PAM implementation is to make sure you have well-defined use cases and user profiles. Use a PAM to assign levels of access for service account management, discovery functions, asset and vulnerability management, analytics, and more.
If your organization does not have the resources to maintain security staff who are trained to install, configure, and manage these solutions, consider using a managed service provider (MSP) who can perform these functions for you.
Perform Continuous Privileged Account Discovery
One of the most important steps to secure privilege access is to identify all valid uses of privilege access to servers, cloud services, databases, and other systems. This ensures that privileged accounts are valid, but also pinpoints accounts that are not. For instance, it’s important to keep track of not only granting but also removing privileges when people move jobs between departments, or when they leave the company.
Privileged accounts should be monitored at all times using automated mechanisms to identify malicious or accidental activity. Analysis of this activity allows you to gain insights into user behavior, ensures that your access systems are up to date, and checks that least privilege is applied correctly.
Knowledge Check
Ready to review what you’ve learned? The knowledge check below isn’t scored—it’s just an easy way to quiz yourself. To get started, drag the description in the left column next to the matching term on the right. When you finish matching all the items, click Submit to check your work. To start over, click Reset.
Great work!
Resources
- External Link: National Institute of Standards and Technology (NIST): Privileged Account Management Guide
- Trailhead: Manage Identity and Access